Hallo, let’s first define what public key and SELinux mean.
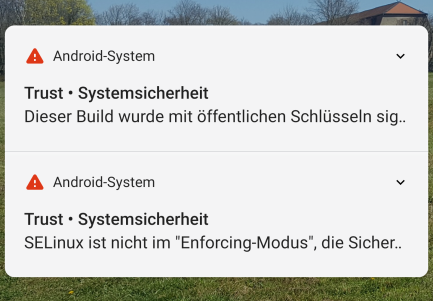
This build was signed with public keys
I found an answer online : Android uses a key to sign apps, but by default, that key is well-known and available in the ROM source tree. Since apps that are signed by those keys and that are installed as a system app can obtain special permissions, a warning was put in place if the default key is used.
SELinux is not in “enforcing mode”, the security is undermined by that.
Here is an explanation of what SELinux is
Kurzgesagt : As part of the Android security model, Android uses Security-Enhanced Linux (SELinux) to enforce mandatory access control (MAC) over all processes, even processes running with root/superuser privileges (Linux capabilities). Many companies and organizations have contributed to Android’s SELinux implementation. With SELinux, Android can better protect and confine system services, control access to application data and system logs, reduce the effects of malicious software, and protect users from potential flaws in code on mobile devices.
Is it a reason to be alarmed?
Yes, both are security flaws. I am however not knowledgeable enough to tell how seriously it impacts security.
Is there anything I can do to fix this?
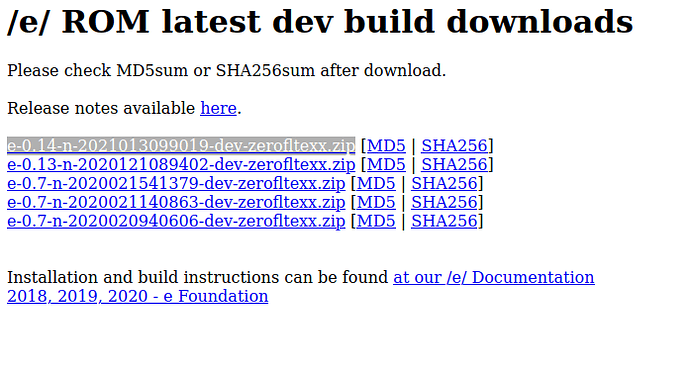
Public key : When it comes to the public key part, I think that a way to fix this would be for the one who built it, @itsclarence to sign his build with his own key.
SELinux : Since what you mention also affects the Q build running on my S6 Edge, I tried to fix the SELinux part following this post. However, using the SELinuxModeChanger app did not work, I think therefore that it probably will not work on your S6 either. I tried various other methods, none of which worked, but feel free to try yourself. I suppose the only way to fix this would be in the building process. I do not know if it has to do with the sources used or something else, maybe people who build can comment to enlighten us.