Hi, I just setup the beta of /e/ on my fairphone 3+, it worked more or less fine, no errors while installing etc. I am used to encrypting my hone after setting it up the first time, but this time the settings tell me that it may already be encrypted. I dont have to enter my lock code before booting it up though. So i am confused. Did the encryption mechanism change in Android 10?
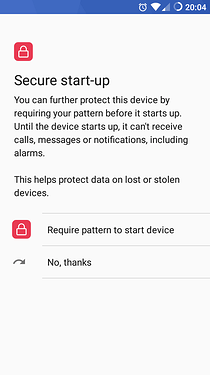
You should enable the secure startup when set a pin, or a password or a pattern.
Encryption by itself doesn’t enable lock
Where do you find the setting? I am on Q and I cannot find it. Search function also doesnt find it.
I’m not on android 10, but I guess you can simply write “Lock” on the search field on Setting menu, and you should see some results, and try one by one
Edit: wait a moment, I’ve just remembered that I have the other spare phone on Los17…
Okay: Settings, Security, Screen lock, PIN, and the first thing it asks is just about Secure start-up.
Of course, if you have already set a pin, you have to remove and do those steps
If I remember correctly “Secure start-up” isn’t something available on FP3.
I searched for it. No such option.
@Anonyme So thats on my phone model then? But I can see that its encrypted in the options. Are there any implications to not having “secure start-up”?
This has to be confirmed, but I think the FP3 comes with some hardware encryption/protection capacities (like every new Android smartphone), so the device is more secure and doesn’t require any password from the user to decrypt the data partition.
So I don’t think it’s less secure (if it was, secure start-up wouldn’t have been removed). It’s still not possible for a third party to access your data without your password/PIN (if the bootloader is locked).
Interesting. Although I cant imagine how to decrypt something without a password at some point 
Maybe somebody has more information on it?
The data partition isn’t encrypted by the password/PIN, if it was the case, each time you would change it the data partition would have to be re-encrypted which isn’t the case.
With secure start-up : the decryption key is encrypted thanks to the password/PIN.
Without : the decryption key is just stored in a safe place in the device and is used each time the device boots.
At least that’s how I see things based on my readings.
So that means somewhere in the internals the key for unlocking the rest of the phone is sitting around?
How does that protect my data at all? It means my data cannot not be read without some TPM like hardware decrypting it? Kind of? So if I would be able to root my phone without deleting the data, I could just read all of it? Doesnt sound so safe in regards of political repression and the resourceful institutions that come with it.
Is there any possibility to add some “Full Disk Encryption”?
Yes because the FP3 is encrypted by default even if you don’t set any password/PIN.
But according to what I know it is stored in a secure environment and even if you are rooted you can’t just access any “decryption_key.txt” file. Same thing for iPhones for instance.
Of course not a single device is perfect and I’m not an expert so I can’t give more details.
Never heard of such a feature.
Ok so to summarize: My phone is hardware encrypted. So as long as I set up a PIN it is reasonably secure. I can see that even in recovery I cannot find my personal data. /sdcard and /storage for example seems to be not mounted.
But it is still possible to boot into recovery and apply system updates, so it would be possible to flash packages. That still feels unsecure. In TWRP I had to enter my password when the phone was encrypted. Is this a TWRP feature that the e recovery is missing?
No, you didn’t have to enter the password.
Yes, TWRP prompts you for the password to decrypt the encrypted data partition in case you want to work with the data in it.
But you can just hit “Cancel” at that point, and TWRP will then happily offer you every feature to work with apart from having access to the data in the data partition (you could format the partition, though).
Ok, good to know, guess I felt safer then I was! Another question then: Would it be possible to root my phone via the recovery? I dont want to do it, but I would like to make sure nobody else does it.
I don’t know.
Rooting nowadays seems to start with installing the Magisk framework using TWRP, so that should be possible at least … https://www.xda-developers.com/how-to-install-magisk/ … but I don’t know whether that’s already “Root” then or just a necessary preparation, or whether other methods to root the phone via recovery remain.
That’s what I think. Again, not an expert, everything is just based on my experience and readings.
Hopefully, yes.
This has to be confirmed. Maybe there is a signature verification that would only allow flashing files provided by the eFoundation. I hope there is, otherwise there would be no difference between a locked bootloader and an unlocked one. Never tested.
That’s because TWRP has more features and allow you to interact with the data partition which is why a PIN/password is asked by TWRP if you want to access to the data partition (but as AnotherElk said you can click on Cancel). The recovery provided with /e/OS for the FP3 has less features and none of them needs to access the data.
In a more classic phone (without a/b partitions, or without the possibility to lock the bootloader), you just have to flash this zip file in TWRP > Install.
The “Magisk Manager” app will then be automatically installed in order to be able to give root access to the apps you want and to install modules you want.
Don’t know if you have to boot TWRP on the FP3 or if this zip file can also be flashed with the built-in recovery.
Thank you so much for the detailed answer! <3
I will go ahead and just test if its possible to install some zip files, for example the fdroid priviledged one, that I anyway would like to use. There shouldnt be any signature from the eFoundation on it. Lets see…
For the root thingy I will first study the a/b thing a bit more since I am a bit confused sometimes about it^^ But when I found out how it all works I will try to root it. Lets hope I cannot manage to do it ![]()