Hi guys,
I want to show you how you can get rid of all things that the developer of Eelo haven’t done yet. In this guide we will do all things to get your Eelo or LineageOS devices safe!
If you want more privacy you can soon buy the Librem 5 > Pinephone or use CopperheadOS > GrapheneOS > EeloOS > LineageOS ordered after privacy fokus.
Don’t worry if you see settings for LOS (LineageOS) because it’s most of the time exactly the same -> Eelo is a fork of this 
What should be done:
- GPS -> In Eelo fixed
- DNS -> In Eelo fixed
- WebView -> Change to BromiteWebview
- Captive Portals
- Privacy Apps
- Hostfile
//Add a “h” to “tttps://” = “https://” for using the links, i don’t know why, but i can’t post a real link here! or and start of the adress remove “/”
First we need root / Magisk for the Setup (Attention: With every Eelo update you must do this again because sadly Eelo Official OS is without root):
- Install EeloOs like in the install documentation from the e-team on the site
- Instal Magisk ttps://github.com/topjohnwu/Magisk/releases/download/v19.3/Magisk-v19.3.zip like the OS: adb sideload magisk.zip after the Rom in TWRP!
- After this enable USB-Debugging in Developer-Options (Tap 7 times on Build-Number in Options)
Assumptions:
- Phone running Eelo, Lineage OS 14.1, 15.1 or 16.0 (note that each LOS version might require a different solution)
- Root access ( Magisk open source)
- No OpenGApps or unofficial addons like microG -> Go in settings and deactivate all -> it’s crap don’t use google services and change your hostname, bluetooth name for privacy to random letters)
- ADB Fastboot needed like in the OS install
- Amaze File Mangaer from F-Droid Store (install too) and go in Settings enable root-rights and hidden files
1) DNS
Eelo set-up: EeloOS is using Quad9 with 9.9.9.9. not the best solution but it’s okay
Default set-up: LineageOS uses AOSP default DNS servers, which are Google’s DNS servers 8.8.8.8.
Solution: Replace Google’s DNS servers with those of a preffered DNS provider (see below for recommendations).
How-to:
LOS 16.0:
Settings > Network & internet > Advanced > Private DNS > Private DNS provider hostname > [enter your preferred DNS provider hostname here. Traditional IP addresses are not accepted in this field, so you need to enter a hostname of a provider that supports DNS-over-TLS (DoT)]
LOS 14.1 and 15.1:
i) Manual edit for each network (works only for wi-fi). Cumbersome and impractical when connecting to more wifi hotspots and unusable when connecting to public hotspots or using mobile data. Wifi list -> Long press select network -> Modify network -> IP settings from DHCP to Static -> Fill out all fields.
ii) Bypass by using a VPN tunnel or Tor (Orbot or orWall). Either a full on VPN (OpenVPN or Wireguard) or a DNS-only VPN DNS66 ttps://www.f-droid.org/en/packages/org.jak_linux.dns66 or 1.1.1.1 ttps://play.google.com/store/apps/details?id=com.cloudflare.onedotonedotonedotone. Simple, but more of a circumvention than solution. Requires background VPN to be constantly on (battery usage increase can be significant).
iii) App ‘DNS man’ on F-Droid ttps://f-droid.org/en/packages/io.github.otakuchiyan.dnsman/. Unmaintained since 2016, but could work -> has 4 setting methods -> try System properties first.
iv) For Magisk users, you can use the CloudflareDNS4Magisk Module ttps://forum.xda-developers.com/apps/magisk/module-cloudfaredns4magisk-t3772375
v) [UNCONFIRMED!] Manual edit of /system/build.prop by adding the following lines
net.dns1=1.1.1.1
net.dns2=1.0.0.1
net.rmnet0.dns1=1.1.1.1
net.rmnet0.dns2=1.0.0.1
net.wlan0.dns1=1.1.1.1
net.wlan0.dns2=1.0.0.1
DNS provider recommendations (get DNS server IP addresses from the sites directly):
- Cloudflare ttps://1.1.1.1/dns/, offers DoT (for LOS 16 Private DNS), global,
- OpenNIC ttps://www.opennic.org/, no DoT, global,
- DNSWatch ttps://dns.watch/, no DoT, Germany,
- UncensoredDNS ttps://blog.uncensoreddns.org/, DoT (on ttp://www.unicast.uncensoreddns.org, Denmark,
- CZ.NIC ttps://www.nic.cz/odvr/, DoT, Czech Republic.
Wikipedia list of DNS providers ttps://en.wikipedia.org/wiki/Public_recursive_name_server
2) Captive Portals
Default set-up: The Captive Portal detection checks for a HTTP 204 code from a Google domain (/connectivitycheck.gstatic.com for LOS 13+)
Solution: Replace Google’s captive portal server with a third party alternative.
How-to: Enter the following in terminal (or use adb - for that method, see German source below) and for the domains pick your preferred option from the list below:
Connect your Smartphone to a PC and use in Terminal (Linux recommend)
Use this code with “adb shell” and “su”:
settings put global captive_portal_mode 0
settings put global captive_portal_detection_enabled 0
settings put global wifi_watchdog_on 0
settings put global wifi_watchdog_background_check_enabled 0
settings put global captive_portal_server f-droid.org
settings put global captive_portal_https_server "https://f-droid.org"
settings put global captive_portal_http_server "http://f-droid.org"
settings put global captive_portal_fallback_url "http://f-droid.org"
settings put global captive_portal_other_fallback_urls "http://f-droid.org"
-> I used f-droid because this is the better choise than the eelo store! Only open source software with no tracking
Select a non-Google server from the following options:
http://captiveportal.kuketz.de
Source, German ttps://www.kuketz-blog.de/android-captive-portal-check-204-http-antwort-von-captiveportal-kuketz-de/). Site and server belong to Mike Kuketz; a German security researcher. Based on his blog and privacy policy, Mike is the genuine article. Reach your own conclusion, but I have zero qualms recommending his server. I also encourage reading through his site and forum (German only). Great posts for privacy-conscious users.
https://e.foundation/net_204/ (if you forget the "/" at the end, it won't work) and http://204.ecloud.global (for http)
Hosted at ScaleWay. These are newly set-up check servers by the people behind the /e/ ROM, which is based on LOS and focuses on user-privacy.
http://elementary.io/generate_204
Hosted at Cloudflare. ElementaryOS is a, dare I say it, game-changing linux distro based off of Ubuntu and which puts heavy focus on UI and UX - think of them as the macOS of linux.
http://httpstat.us/204
Hosted at Microsoft’s Azure. Site created by two US IT professionals. Claim no data stored.
Further reading on Android captive portals with explained commands is here ttps://android.stackexchange.com/questions/100657/how-to-disable-captive-portal-detection-how-to-remove-exclamation-mark-on-wi-fi and here ttps://android.stackexchange.com/questions/186993/captive-portal-parameters.
Notes:
- Do not use /connectivity-check.ubuntu.com as previously suggested. It does not work correctly, is hosted on Google Cloud and the Ubuntu community (not only on reddit) is quite touchy when you try to raise this issue and suggest they self-host.
- whatever server you choose (and yes, you can make one yourself), make sure it returns a HTTP 204 code (use curl -I to make sure)
3) A-GPS
Eelo set-up: With the Mozilla Location Service the eelo-team had done a great job -> the only thing you shoud change is: disable all microG-Features in Settings and Disable all GPS connection with MobileInternet and Wlan in the location settings to be save.
Default set-up: LineageOS defaults to /supl.google.com for SUPL data ttps://patents.google.com/patent/US20150005006, which helps in speeding up device positioning (aka TTFF) when using A-GPS, but each request to server is accompanied by device’s IMEI.
Solution: replace every mention of Google’s A-GPS SUPL servers in /system/etc/gps.conf with that of one of the following servers. Apparently, disabling A-GPS and using GPS only might not help. Sadly, very little credible research exists on this topic. Firewalling GPS is also a possible solution. Note that this increases TTFF, as it relies solely on GPS sattelite signal instead of local cell tower data.
Servers found:
- /supl.sonyericsson.com - Working (port 7275 is open), located in Ireland, hosted with Amazon.
- /supl.vodafone.com - Working (port 7275 is open), located in Germany, self-hosted.
- /agpss.orange.fr - live, but port is filtered, located in France, self-hosted.
- /agps.supl.telstra.com - live, but port is filtered, located in Australia, self-hosted.
- /221.176.0.55 - default Xiaomi SUPL server IP, belonging to state-owned China Mobile and hosted in Beijing. Please share if you voluntarily choose this over Google.
Further reading: There’s a very good post on the privacy aspects of A-GPS ttps://blog.wirelessmoves.com/2014/08/supl-reveals-my-identity-and-location-to-google.html and how the gps.conf route might not work, as some GPS chips bypass the OS completely, so I recommend a read through that. This is followed up by a German blog post ttps://www.kuketz-blog.de/android-imsi-leaking-bei-gps-positionsbestimmung/. That said, there is surprisingly very little information on this topic given the severity of the privacy implications.
Note:
- SUPL is not the same thing as NLP (Network Location Provider), which is not present on LOS without GAPPS
- For anyone wondering, Advanced Mobile Location (AML, which Google calls Emergency Location Service; ELS) will become compulsory in the EU in 2020 and should not be present in LOS, because it is a part of Google Play Services
- As linked above, this might not work for all devices, as some have SUPL running on the GPS radio level, which means that anything you do on the Android OS level will have no effect
- both /supl.nokia.com and /supl.iusacell.com are confirmed offline
4) AOSP Webview
Default set-up: LineagOS uses ‘AOSP Webview’ (listed under ‘Android System Webview’ in Apps) - this is different to Chrome, which handles Webview in Android 7 onwards - but AOSP Webview, like the Chromium browser, is open-source but not fully degoogled - although it is better than the proprietary Chrome.
Solution: Replace AOSP Webview with a more degoogled impletentation; Bromite’s SystemWebView ttps://www.bromite.org/system_web_view.
How-to: Download Bromite SystemWebView apk, (from their F-Droid repo or directly), and then follow the official installation instructions ttps://github.com/bromite/bromite/wiki/Installing-SystemWebView.
- Install Bromite with the Magisk Module in Downloads section (Only works with some LineageOS devices, so do the next steps but do this point also, can’t be wrong)
- Install Amaze FileManager from F-droid store (Install this store too)
- Load the Bromite Webview from the Page with your mobile device (The Site generate the file you need for your phone
- Rename it to BrowserWebView.apk for Eelo (For LineageOs webview.apk)
- Connect device to pc and write “adb shell” than “su”
- now use the command:
For Eeelo: "mv /storage/emulated/0/Download/BrowserWebView.apk /system/app/BrowserWebView
For LineageOS: "mv /storage/emulated/0/Download/webview.apk /system/app/webview - Restart device and use Webview Test Apk from the ApkMirror
- Choose Html5-Site and https and the result should be chrome74 with galaxy s9 for example not your real phone device!
5) Project Fi
Default set-up: Certain [Project Fi devices ttps://en.wikipedia.org/wiki/Google_Fi#Devices have extra Google apps to function properly ttps://old.reddit.com/r/LineageOS/comments/823m9r/why_do_i_still_have_google_connectivity_services/.
Solution: Remove Project Fi apps for those LineageOS users that are not Project Fi customers
WARNING: Uninstall system apps at your own risk (may cause system crash)!
How-to: Uninstall the following apps using a (root-requiring) system app removal tool of choice or via adb (instructions ttps://www.xda-developers.com/uninstall-carrier-oem-bloatware-without-root-access/):
X Google enrollment (/com.android.hotwordenrollment.xgoogle)
T Google enrollment (/com.android.hotwordenrollment.tgoogle)
OK Google enrollment (/com.android.hotwordenrollment.okgoogle)
Tycho (/com.google.android.apps.tycho)
Google Connectivity Services (/com.google.android.apps.gcs)
Carrier Services (com.google.android.ims)
source ttps://github.com/lineageos4microg/l4m_website/issues/16#issuecomment-374364988
Presence of the above apps on following devices:
| Device | X/T/OK Google enrollment | Tycho | Google Connectivity Services | Carrier Services |
|---|---|---|---|---|
| Google Pixel XL (marlin) | yes | |||
| Google Pixel 2 (walleye) | yes | yes | yes | yes |
| Google Pixel 2 XL (taimen) | yes | yes | yes | yes |
| Google Pixel C (dragon) | yes | yes | ||
| Google Nexus 6P (angler) | yes | yes | yes | yes |
| Google Nexus 5X (bullhead) | yes | yes | yes | yes |
| Essential PH-1 (mata) | yes | |||
| Google Nexus 6 (shamu) | yes | yes | yes | |
| Motorola Moto X 2015 (clark) | yes | |||
| Motorola Moto G4 (athene) | yes |
Source ttps://github.com/lineageos4microg/l4m_website/issues/16#issuecomment-374491502
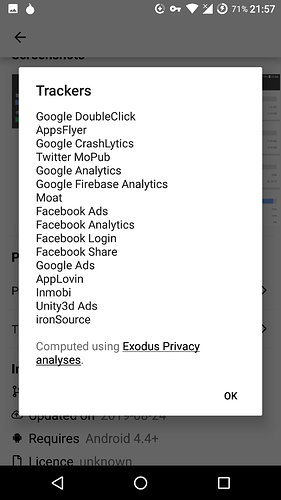
6) Privacy APKs
- AppStores: Use F-Droid store first, than Eelo-Store for non free Apps (like for your bank) and the yalp-Store if you want all apps like in the goolge store with the google repo (Eelo store isn’t full of apps)
- Privacy: Use a VPN like from f-Droid Store, Only payed VPN-Provider deliver good Speed or better Orbot + use K3pler Apk and set a proxy on localhost:8090 so you can check connections and block them + Adblock plus apk with root to block ads and load the app Launch on boot from apkpure at set it for k3pler, because k3pler wont start with boot
- Chat & Messaging : Change in the Settings the SMS/Phone application because Signal isn’t a great app, look here: ttps://www.securemessagingapps.com/ -> Using Threema (not open source) or Wire open source is a better solution with less tracking. Never use apps / services from USA, the privacy laws there a very bad and NSA loves your data -> Better germany/switzerland. The best solution is nextcloud with a good server you can choose by yourself or xmpp-application like https://f-droid.org/en/packages/eu.sum7.conversations/. Best for privacy if you host on your own nas / router a server and use this with nextcloud or xmpp for all your people you chat with!
- With ttps://f-droid.org/en/packages/de.j4velin.systemappmover/ you can remove apps, if you have root, like telegram and signal
 , remove the bad system apps!
, remove the bad system apps! - Good to know, you can install the eelo-appstore on other androidOS system like for LineageOS. Here is the APK i made with Amaze!:
https://www97.zippyshare.com/v/EFwoOHqC/file.html
7) Host-File:
- Use the Amaze filemanager to find the host file in /system/etc/host.conf and edit it with it
a blocked adress should look like this
127.0.0.1
127.0.0.1 …
…
Here a list of my blocked sites i found with k3pler:
/google.com/gen_204
/accounts.google.com:443
/connectivitycheck.gstatic.com/generate_204
/google.com:443
/s3.amazonaws.com:433
/collector-hpn.ghostery.net:443
/cmp-cdn.ghostery.com:443
/api.ghostery.net:443
/cdn.ghostery.net:433
/updates.signal.org:433
/googleads.g.doubleclick.net:433
/fonts.googleapis.com:433
/api.cleanapk.org:433
/clientservices.googleapis.com:443
/ssl.google-analytics.com:443
/bahn.de:443
/deutschebahn.sc.omtrdc.net:443
/assets.adobedtm.com:443
/cdn.optimizely.com:443
/settings.crashlytics:443
/firebaseremoteconfig.googleapis.com:433
/graph.facebook.com:433
ttp://xtrapath1.izatcloud.net/xtra3grcej.bin
ttp://xtrapath2.izatcloud.net/xtra3grcej.bin
ttp://xtrapath3.izatcloud.net/xtra3grcej.bin
-> Last privacy advice:
Use VPN + Adblock in your openVPN Router (TurrisOmnia/GLiNet are good) or on your phone.
-> Best AndroidOS are: Replicant > CopperheadOS > Eelo > LineageOS (Best Linux Phone Librem 5 / Pinephone)
-> Use a Linux PC with no IntelManagmentEngine like lenovo x200 with coreboot changed wifi > Librem 13/15 > Normal PC with Linux but Intel ManagmentEngine
Links:
ttps://www.reddit.com/r/degoogle/comments/clcgtl/degoogling_lineageos_instructions_august_2019/