this issue is related to https://github.com/microg/GmsCore/issues/1939
microg embed as privileged app the google/Apple “exposure notification” API, which is a privacy and security flaw.
such tracker don’t require privilege level and enforcing it at system level is as problematic as Analytics due to the fact it collect user data (even in encrypted form, as long as you know the format of data and you have sufficient data collected, cryptography is weak against such attack)
microg chosen to follow google terrorism and enforce it upon user that install it, when for exemple they were more pro-active upon freedom with NLP design allowing the user to select the NLP provider they want (and even use fully local NLP)
the “exposure notification” is a feature that was in the paper “region based” but enforced even on region that don’t support this, this enforcement is first suspicious key
second suspicious key is the fact the enforced it at system level, when other, as effective, solutions were done at user level
system level enforcement is problematic, because in android, system has even more rights that the human user, unless you rooted the phone, the system is the full master of the phone. This create a security flaw, and even if the source can be carefully reviewed there is still security exploit that can arise.
google and apple promised they will sunset the technology when THEY decided it’s no more needed, it’s more than a year that this technology is no more required, neither widely used, and most “contact exposure trackers system” are now closed, but THEY decide it will be still there, same for microg team
exposure notification has some obvious flaw like “reverse tracking” as noted by the electronic fundation, which is the most obvious attack, but, at a time where even whatsapp metadata is sold billions dollars, when it only contain the “who you contacted” information, imagine what it could be done with “who you were nearby info”, anomysation is a lie, european RGPD only constrain personal information aggreement, access and deletion if the personal information if not anomimazed, the issue is that there is no need to actually know your real name, an ID is sufficient, you’re “HUMAN#118265902” and if any software piece know you as such, your real name is no importance, and the bluetooth mac “randomization” and “daily keys creation” isn’t sufficient to warrant no tracking possibility, a day of data collection (when 15 min of wifi data collection is sufficient to break the key) is far enough to make the use of crypto “candy sugar” and even can have the reverse effect because of the change of bluetooth mac, which can be correlated with RSSI information to identify with good probality what device changed it’s mac, then create a “before MAC, after MAC, crypted message” database and then use a device that have google localisation services activated to gather the remaining “GPS precise localisation” information that is missing to have as good as a 10 year old GPS localisation precision…
as I said, if google/apple/huawei didn’t enforced it at system level, and that the user have the right to install it and remove it when they feel they don’t need it, it is user choice. because they enforced it and are sole master of what they do with it is even more suspicious. AND because they remain the “only one check point” they have all the information to go back to the original information… even if microg team don’t provide to google/apple/huawei all the information, the fact they comply with the beacon sending allow other google/apple/huawei to report information about us.
as long as data is collected, even if in “theory” they says it remain on user device (and in theory they said whatsapp won’t sell metadata, they said microsoft don’t harvest personnal information, and google said they don’t read your mails) you can’t be sure, and all phone embedding the technology might act as a spy without knowing it, which is problematic.
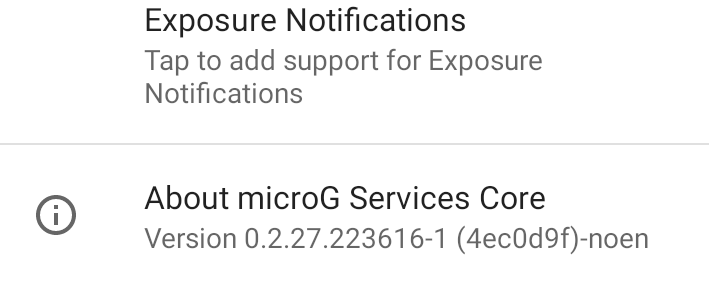
microg is a bit more secure than google apps which are closed source, but for me, this api is no more needed, has too much privileges and I don’t want to “maybe” become a “gogol spy bot”… so I just don’t want it installed, even if I can desactivate it, as long as the code is there, it can be activated.
neither I want to promote the technology, as I said, enforcing upon people is by nature problematic
microg team don’t want to make it optional and then want to enforce it upon us (and more, want to keep it active “just in case” it might be usefull in future) which is same as google/apple policy. Such behavior is cracking my trust, hopefully the code is opensource and I can fork it and remove this part.
so my question : if I fork the project, remove all the related code (or build my version of microg without support of this, as it might be possible to do so) and build my own version, will I be able to overwrite the version installed by default?
thanks and regards
Regain your privacy! Adopt /e/ the unGoogled mobile OS and online services